
Logjam Vulnerability Advisory
This is a security advisory on the “Logjam Vulnerability.”
What is Logjam Attack
The Logjam vulnerability is a weakness that left secure sites open to attack. A weakness in encryption protocol called Diffie-Hellman is letting attackers downgrade certain connections to 512-bits of security which is low enough to be cracked by attackers. At this time it’s not clear if anyone is actively exploiting the weakness.
Attackers with the ability to monitor the connection between an end user and a Diffie-Hellman-enabled server that supports the export cipher can inject a special payload into the traffic that downgrades encrypted connections to use 512-bit key material. Using precomputed data prepared ahead of time, the attackers can then deduce the encryption key negotiated between the two parties.
This vulnerability is a flaw in the SSL/TLS protocol and has been present for more than 20 years, affecting HTTPS, SSH, IPsec, SMTPS, and protocols that rely on TLS, so the vulnerability is very widespread.
However, to take advantage of this vulnerability, an attacker needs to be on the same network as the victim, such as on the same Wi-Fi network.
Who is Affected
- All Websites, mail servers, and other TLS-dependent services that support DHE_EXPORT ciphers are at risk for the Logjam attack.
- Websites that use one of a few commonly shared 1024-bit Diffie-Hellman groups may be susceptible to passive eavesdropping from an attacker with nation-state resources.
How ControlCase CaaS Customers can request a test for Logjam Vulnerability
ControlCase Compliance as a Service (CaaS) customers can request “GHOST Vulnerability Scan” by using the following steps:
-
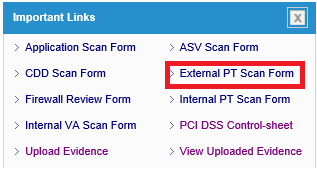
- Login to IT GRC portal
- Click “External PT Scan Form” link on the dashboard
-
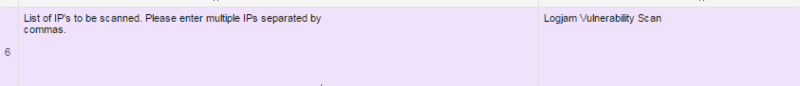
- Fill the External Penetration Test form with all the details and mention “Logjam Vulnerability Scan” before filling the public IP addresses against #6
-
- Once form is filled completely, click Notify button on top right corner
![]()
How to test if you are vulnerable
The easiest way to check vulnerability is to check SSL configuration and ensure that DHE_EXPORT ciphers are not supported by the server.
How to fix
The best way to mitigate the risk is to deploy Diffie-Hellman correctly for TLS by following below implementation:
- Disable Export Cipher Suites
- Deploy (Ephemeral) Elliptic-Curve Diffie-Hellman (ECDHE)
- Generate a Strong, Unique Diffie Hellman Group
- Make sure any TLS libraries in used are up-to-date and that rejects Diffie-Hellman Groups smaller than 1024-bit.
It is recommended to ensure that the most recent version of browser is installed, and check for updates frequently as Google Chrome (including Android Browser), Mozilla Firefox, Microsoft Internet Explorer, and Apple Safari are all deploying fixes for the Logjam attack.
References
https://weakdh.org/sysadmin.html
http://thehackernews.com/2015/05/logjan-ssl-vulnerability.html