ControlCase Data Security Rating
 While standards such as PCI DSS, ISO and SOC provide a benchmark for protecting data, criminals are always on the hunt for security vulnerabilities and malware to exploit organizations.
While standards such as PCI DSS, ISO and SOC provide a benchmark for protecting data, criminals are always on the hunt for security vulnerabilities and malware to exploit organizations.
The ControlCase Data Security Rating is focused exclusively on understanding your environment and providing solutions that seamlessly integrate security and go beyond just compliance.
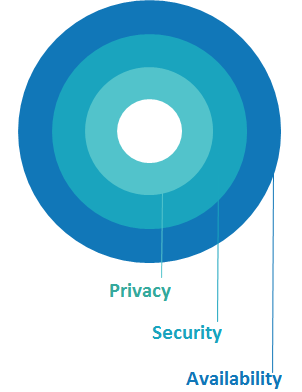
In simple terms, it is a rating of your IT system based on three major categories: security, privacy and availability. As part of that, it provides a remediation plan with clearly delineated priorities and cost estimates. We aim it explicitly at a non-IT specialist audience, so that the Board and other stakeholders can understand how secure and compliant your company’s IT systems are.
The Value Proposition
The ControlCase Data Security Rating will use compliance as a lens to see how vulnerable your systems are to a breach. The average cost of a data breach is $3.6 million. Companies face 27.7% chance of a recurring material data breach over the next two years.
The ControlCase Data Security Rating aims to capitalize on your current compliance and security investment by actually monitoring and analyzing the data you collect. We will tell you how you can avoid breaches and what it will cost to do so using this data.
Not only will it help you reduce your system’s vulnerabilities, it should also help you prepare for your audits. For example, if we find significant problems in availability of your systems, we will tell you how to fix that before the auditors come in.
What Is The ControlCase Data Security Rating?
 It is a comprehensive review of your own data in order to provide a clear rating that both non-specialists and specialists can understand. And it comes with a specific and complete remediation plan with cost estimates, prioritized according to a rigorous cost-benefit analysis. Once set up, it will provide continuous monitoring of your system using real-time data to make sure that vulnerabilities are mitigated and that any changes in your system do not compromise its security, availability or privacy.
It is a comprehensive review of your own data in order to provide a clear rating that both non-specialists and specialists can understand. And it comes with a specific and complete remediation plan with cost estimates, prioritized according to a rigorous cost-benefit analysis. Once set up, it will provide continuous monitoring of your system using real-time data to make sure that vulnerabilities are mitigated and that any changes in your system do not compromise its security, availability or privacy.
As part of that our quarterly deliverable will be comprised of two parts.
First, we provide an easy-to understand score of your system. It is very much like a bond rating, except for your security system. As part of this, we will also rate your company in the three major categories: security, privacy and availability.
Second, beyond just the rating, we also provide a remediation plan to decrease the chance of breaches. This will include estimated costs so that you can you prioritize your spending. This is real data that can be used to justify your security budget.
The service comes with an easy-to-use dashboard with the ratings, remediation points and constant updates on whether the vulnerabilities have been mitigated or not. The IT team will clearly be able to identify their needs quickly and easily.
UNIQUELY BASED ON OUR LONG HISTORY OF TESTING
The ControlCase Data Security Rating is based on what we have learned providing compliance services for more than a decade with over 1,000 customers. We understand where and why IT systems are vulnerable. We also base our rating and all of our recommendations on your own data, which we believe is a better indicator of strengths and weaknesses than other methods.
We are building this new product from scratch with the goal of letting non-IT specialists easily understand their company’s IT strengths and weaknesses. We promise: No jargon, no hard-to-understand terms.
OUR ANALYSIS LIMITS THE EFFORT ON YOUR SIDE
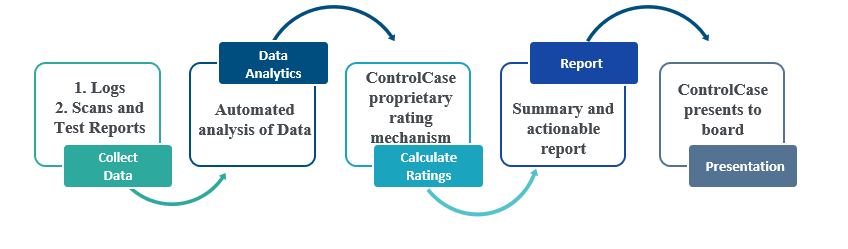
We take significant raw data from your company’s systems that we then analyze to ascertain the vulnerabilities of your system and what needs to be done to fix it. Once the initial feeds are set up, we expect the gathering of the data to be done automatically, so that there is limited time and effort needed on your side.
We promise to keep our data requests minimal and generally what you already have, including raw data that needs no formatting.